What checkm8 means for stalkerware on iOS

On Friday, September 27th 2019 many of us on the mobile security community were surprised with the news of a SecureROM vulnerability disclosed on Twitter by @axi0mX. axi0mX described it as "a permanent unpatchable bootrom exploit for hundreds of millions of iOS devices" and called it checkm8 (read 'checkmate'). Here are two articles (one and two) explaining very well the implications of this disclosure for the future of iOS jailbreaking and security research as well as clarifying some of the confusion around what it can and can't do.
IMO checkm8 is wonderful news. It will help the research of a lot of security experts and this will make iOS a better and more secure OS. Yet, as almost any new discovery, it can be used to do good and bad purposes. On this post I'm going to focus on what it means, again in my opinion, for the future of stalkerware (a.k.a. spouseware) on iOS.
tl;dr checkm8 gives attackers a very powerful tool to deploy malicious applications to spy on users. However, there's a very easy way to stop this attack: users simply need to reboot their device.
What attackers CANNOT do
The very first point you need to know is that this vulnerability cannot be exploited remotely. There's absolutely no way to exploit it remotely since the device has to be set in DFU mode (by holding 2 physical buttons on the device for a couple of seconds) and then a USB cable connected to the device that performs the exploit.
This vulnerability doesn't allow them access to the SEP (Secure Enclave Processor). The SEP is responsible to protect your biometrics data for Touch ID and Face ID as well as your device PIN or password. This means this exploit won't allow an attacker to perform brute force attacks on your PIN or password. In other words the exploit doesn't give them access to your data unless they know your PIN or password.
Finally, without going into too much technical details, this exploit is performed in memory. This means that a reboot of the device will "invalidate" the exploit and the device will not boot or load any malicious code (deployed using this vulnerability). In other words, if a device runs out of battery or is manually restarted, the regular boot chain will make sure that only Apple-signed software is loaded.
What attackers CAN do
With this exploit, attackers will be able to load a custom version of iOS. In this customized version of iOS attackers can modify virtually any part of the operating system as well as include their own code. Theoretically they could add a spying application that runs in the background with no UI, no permissions restrictions and be able to collect as much data as they want from the most popular social media and messaging applications. Essentially this vulnerability opens the door for a very powerful spying software to be introduced at the very low level of the operating system.
This is a tethered exploit, which means it needs a computer to be connected to the device in order to exploit the vulnerability. As explained before, the device also needs to be set in DFU mode. All of this means physical access is necessary for this exploit to work, sadly this is very often the case with stalkerware/spouseware, where the attackers have a lot of time alone with the victim's device.
Finally, the range of devices affected by this vulnerability is large. These are the devices that can be targeted with this exploit include:
- Phones from the 4s up to the iPhone X
- iPads from the 2 up to the 7th generation
- iPad Mini 2 and 3
- iPad Air 1st and 2nd generation
- iPad Pro 10.5-inch and 12.9-inch 2nd generation
- Apple Watch Series 1, Series 2, and Series 3
- Apple TV 3rd generation and 4k
- iPod Touch 5th generation to 7th generation
What YOU can do
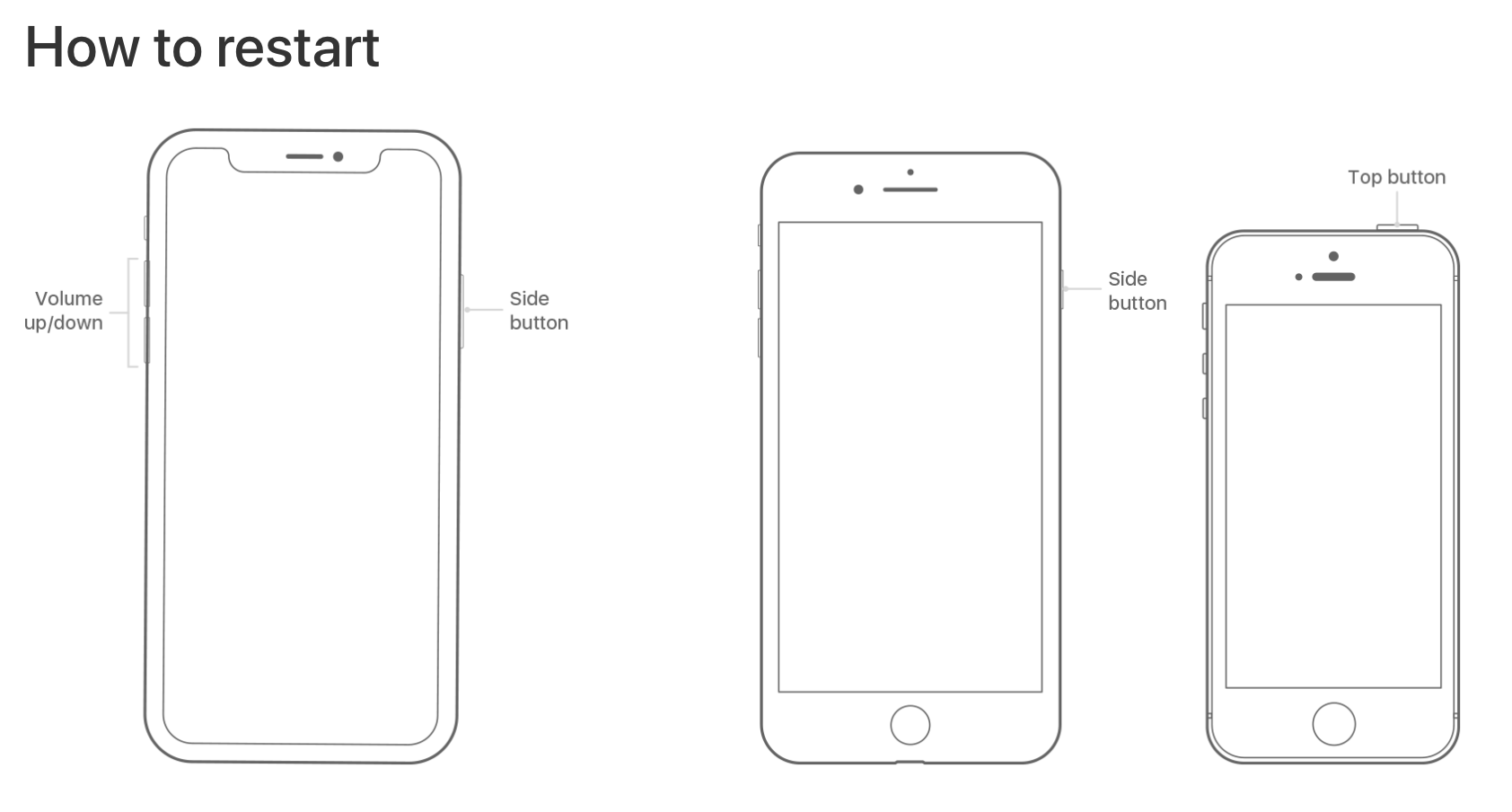
Identify a compromised version of iOS might be difficult for most users. But there's good news, a simple device restart will stop any rouge software installed on the device using this vulnerability. Here's Apple's guide to restart your device.
As I've said before, if you suspect something, this step is easy to perform and will thwart the attacker's efforts because they cannot persist their malicious code on your device.
Be vigilant of changes in the duration of your battery. If all of the sudden your device needs to be charged more often, better be safe and restart it.
To be 100% sure, you can restore your device to a stock OS version by following Apple's guide.
Conclusions
checkm8 will be very beneficial to security researchers and in the end it will help Apple because more research (outside their own) will be done on this already hardened platform. Even so, there are bad people that will try to use it for harm others and this is were people have to be vigilant but also part of my research is dedicated to shed a light on their trends and new attacks.
If you see anything that's incorrect please let me know (@ivRodriguezCA) and I'll fix it.
