Introducing security.plist
tl;dr It's like security.txt but for iOS applications.
As probably you know by now, I spend a lot of my free time reverse engineering iOS applications. But when I find a vulnerability in one of them, it's a very, very difficult process to figure out how to contact the company. More often than not, I have to write an email to a generic info@company.com or fill out a form on the company.com/contact website. Most of these channels are handled by people in marketing or sales, who might have no idea how to respond, what to do or even to identify if it's a real problem.
This is a common problem not just for mobile security researchers, but for all security researchers. This is why some very smart people created security.txt for websites. security.txt solves this problem by creating a text file with all the information a security researcher can use to contact a company about a potential vulnerability found in their system.
What I'm proposing is exactly the same but for iOS applications. We could technically use the same approach as security.txt and embed a text file with all this information. But to keep this file very iOS-like, I thought why not use a property list for this purpose.
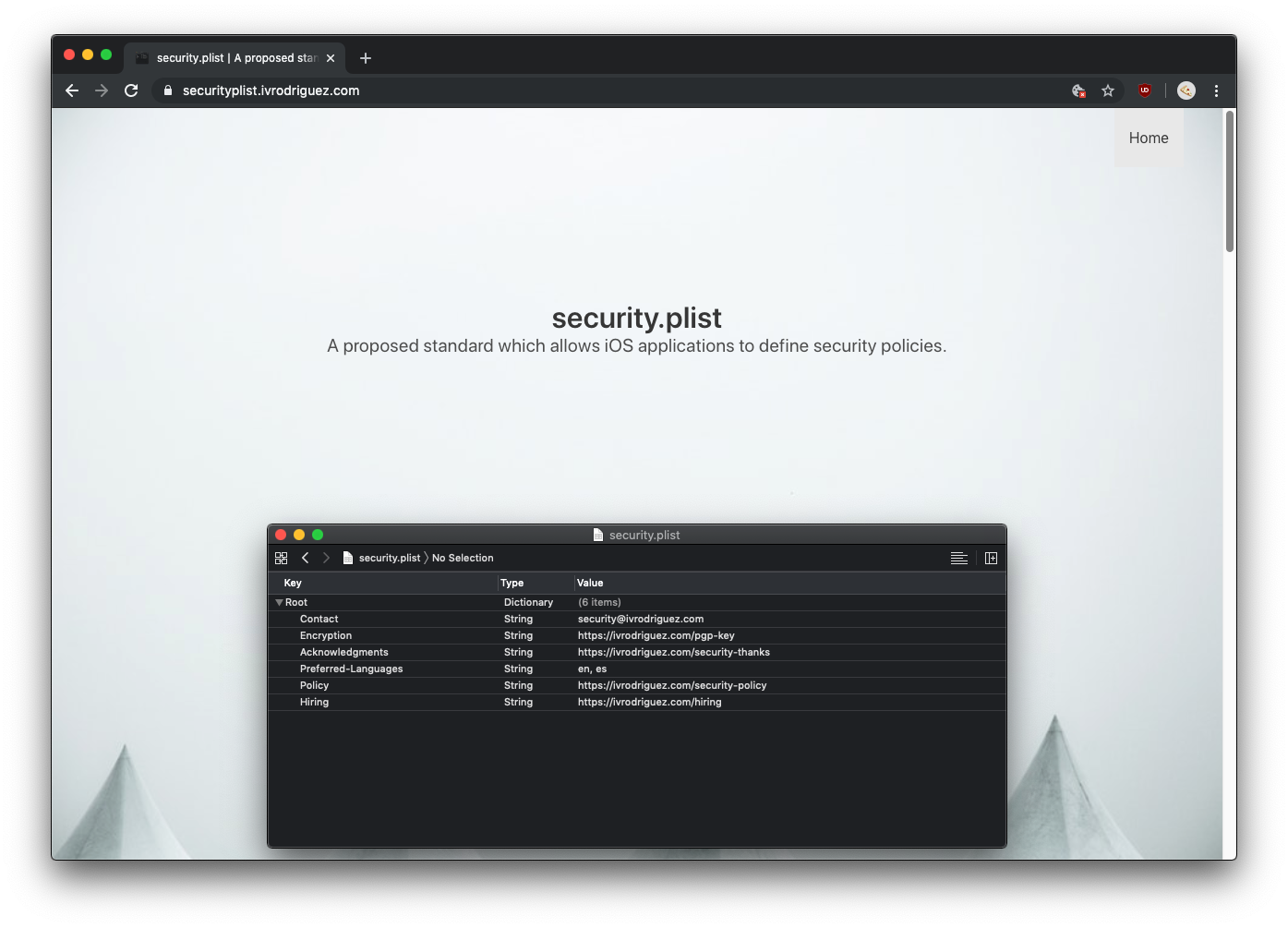
Most (if not all) of iOS developers are familiar with property lists files, Xcode includes a great viewer and editing features for .plist files. This makes security.plist a great candidate to be used to transmit this information.
Since security.txt's website is open source, I forked it and modified for security.plist and you can use it to generate your own security.plist files and add it to your Xcode projects.
You can access the website at https://securityplist.ivrodriguez.com, here's an example of a security.plist:
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<key>Contact</key>
<string>https://ivRodriguezCA</string>
<key>Encryption</key>
<string>https://ivrodriguez.com/pgp-key</string>
<key>Acknowledgments</key>
<string>https://ivrodriguez.com/security-thanks</string>
<key>Preferred-Languages</key>
<string>en, es</string>
<key>Policy</key>
<string>https://ivrodriguez.com/security-policy</string>
<key>Hiring</key>
<string>https://ivrodriguez.com/hiring</string>
</dict>
</plist>
